Researchers have developed a federated learning framework to help smart grids detect DDoS attacks without exposing users’ energy profiles, paving the way for privacy-respecting 6G-era cybersecurity.
As next-generation 6G networks promise ultra-fast, ultra-dense communications, power grids are also evolving, adding edge devices, automation, and AI to manage increasingly complex energy demands. But this hyperconnectivity introduces new risks, especially from distributed denial-of-service (DDoS) attacks that can compromise grid stability or hijack consumer devices.
To counter this, Singapore University of Technology and Design (SUTD) researchers have developed a federated learning framework for smart grids that can detect DDoS attacks in real time, without exposing users’ private energy consumption data. Their study in Cybersecurity outlines a hybrid architecture combining cloud analytics with privacy-preserving local model training to safeguard both data and infrastructure.

Grid cybersecurity. Adapted from images used courtesy of Canva
Smarter Grid, Smarter Threats
Smart grids rely on data like usage patterns, device telemetry, and behavioral trends, which feed into prediction engines that optimize power flow and detect anomalies. But centralizing that data for training or security analytics introduces privacy concerns, especially as smart meters and edge devices track activity at a building level.
Federated learning sidesteps that. It trains models locally, on-device or at the edge, and only transmits model weights or gradients, not the underlying raw data, to the central server. In the SUTD framework, each node in the grid (such as a smart meter or substation) trains a local neural network on its own traffic patterns and sends only the model updates to the cloud, where the network assembles a global model and shares it back.
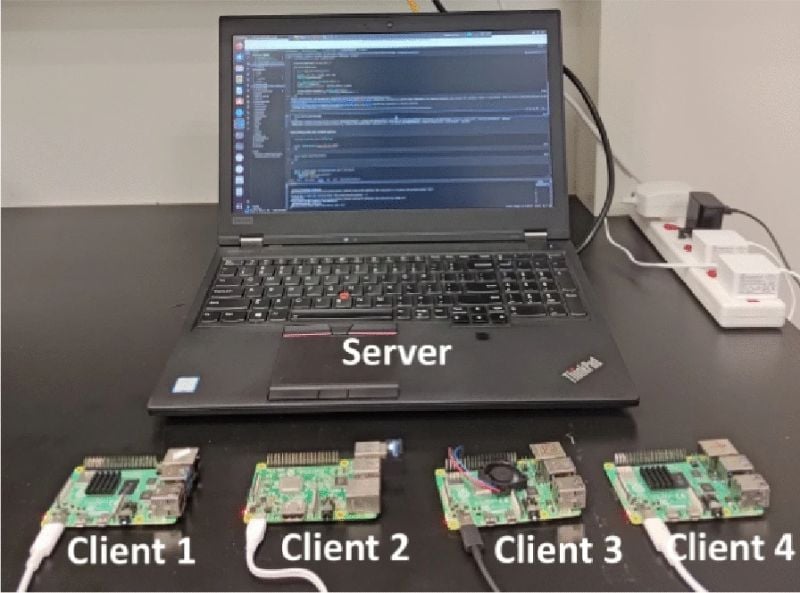
The researchers’ experimental setup. Image used courtesy of Jithish et al.
This setup enables a privacy-preserving collaboration whereby all devices contribute to the security model, but none reveal their own consumption behavior or network logs. In a grid context, this is particularly valuable, since revealing fine-grained load profiles could also reveal when users are home, what appliances they use, or even which electric vehicle charging systems are connected.
Simulated Attacks and Real-World Data
To test their framework, the team used a smart grid DDoS dataset and simulated both normal and malicious traffic at different attack intensity levels. Each node trained on a portion of the dataset locally and then used federated averaging to contribute to the shared model. The primary task was to detect whether incoming packets represented benign communication or a coordinated denial-of-service attack.
The results were promising. Using a bidirectional LSTM network architecture—a good fit for time-series traffic analysis—the system reached an average detection accuracy of 98.6%. It maintained this performance without ever collecting or centralizing raw usage data. Even with up to 30% of edge devices under attack, the federated system could converge and correctly identify malicious behavior, highlighting its resilience in compromised environments.
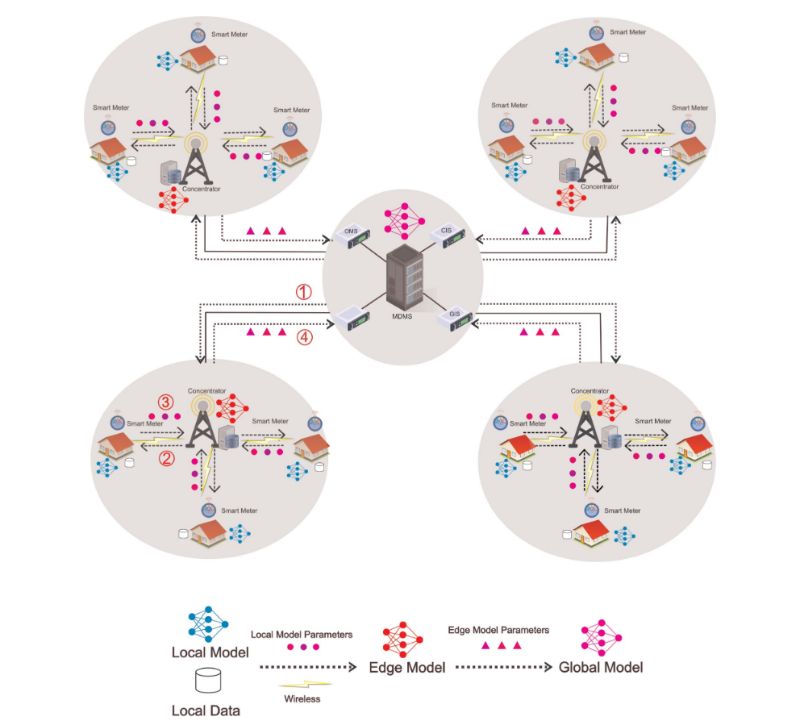
A hierarchical federated learning architecture for attack detection in 6G-enabled smart grids. Image used courtesy of Jithish et al.
The researchers also benchmarked the model against traditional centralized learning. Although centralized models performed slightly better (~0.5% increase in accuracy), they required full data aggregation, which is an approach that simply may not scale or meet future regulatory requirements for user data privacy.
Federated Cybersecurity for 6G Grids
The SUTD team’s research represents a larger shift in grid security from static rule-based systems to AI-driven, adaptive security layers that can scale with the complexity of future infrastructure. In a 6G-ready context, where latency is sub-millisecond, device density is massive, and machine-to-machine communication dominates, centralized cybersecurity becomes not just a privacy risk, but a bottleneck.
Federated learning offers a solution aligned with this future. Keeping training local reduces bandwidth requirements, preserves privacy, and enables real-time, decentralized threat detection. The authors also propose future extensions such as integrating blockchain for trust validation between nodes, applying differential privacy techniques, and using transfer learning to adapt across different grid segments or geographies.
The system is also inherently scalable. As grids expand to include more distributed energy resources, EVs, and demand-response systems, each new node can contribute to the learning process without introducing new security vulnerabilities or increasing exposure.


